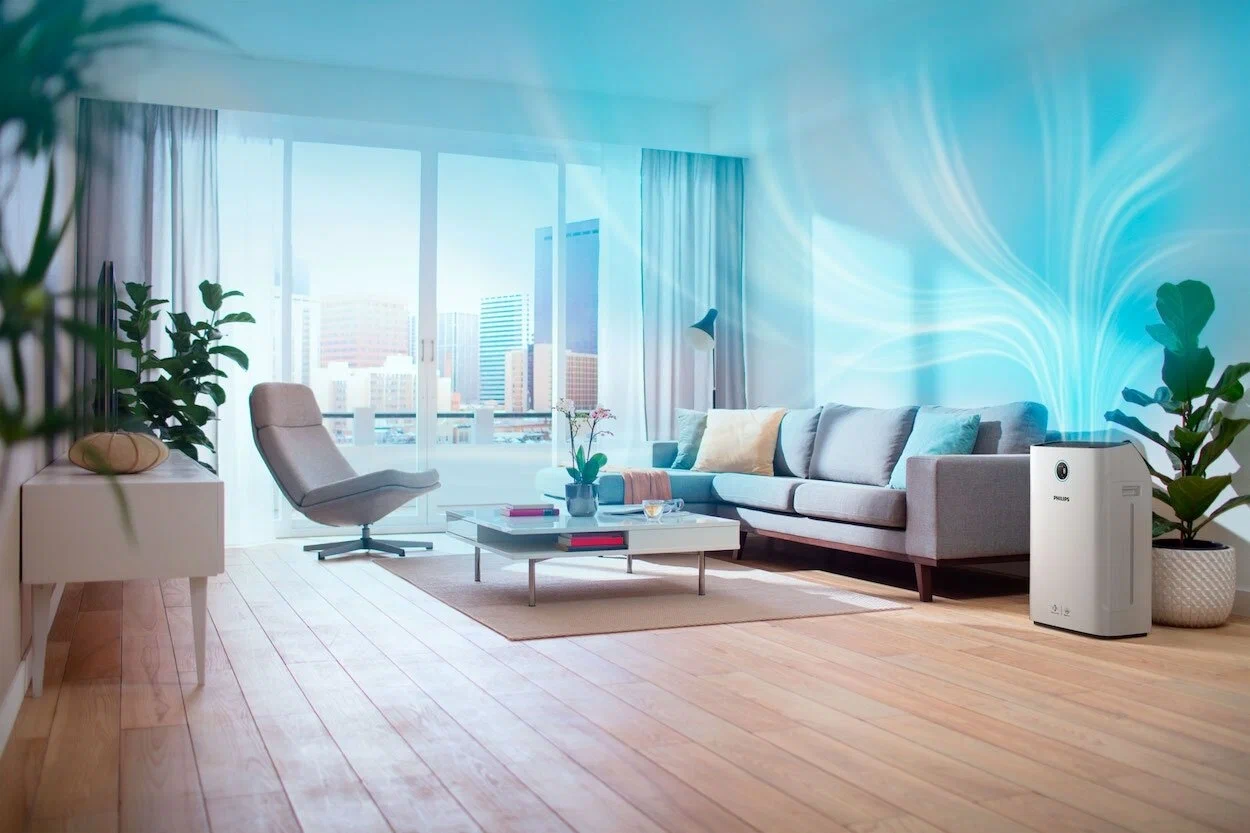
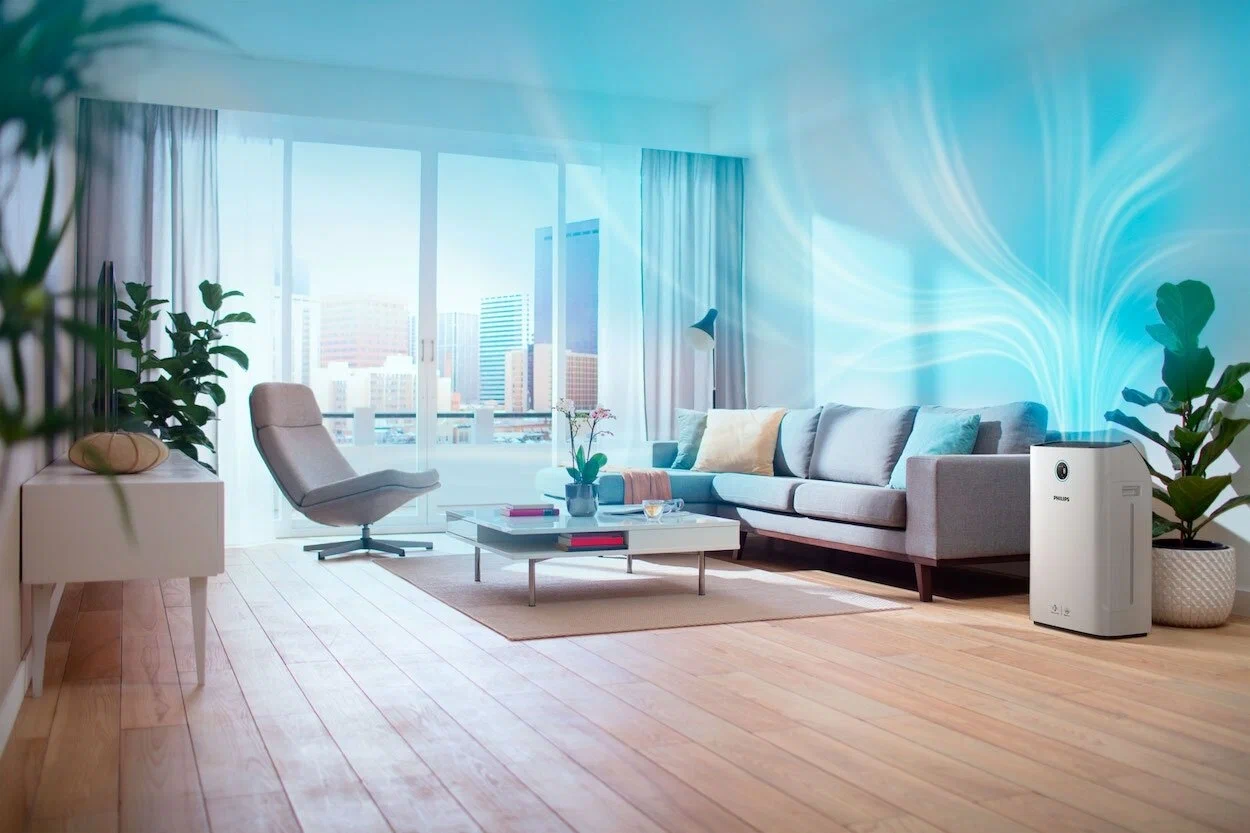
Transforming Spaces, One Breath at a Time
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
![[Combolist.top] 950k Combo list anonfile.txt](https://akron.ai/assets/img/01.jpg)
![[Combolist.top] 950k Combo list anonfile.txt](https://akron.ai/assets/img/02.jpg)
![[Combolist.top] 950k Combo list anonfile.txt](https://akron.ai/assets/img/03.jpg)
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
Our WELL-compliant monitors deliver highly accurate sensor readings, feature Wi-Fi connectivity, and boast a sleek glass finish that complements any interior
Our best in class high efficiency, high performance EC fans are ideal for purified air ventilation

Our WELL Compliant sensors are best in class and provide the needed accuracy to get any project certified

Market Leading efficiency with minimal heat emissions and perform well even at partial loads

Our monitors allow for demand control ventilation making the overall system very energy efficient while maximizing occupant comfort

Our Wi-fi enabled AQI monitors are tightly integrated with our EC fans, providing unparalleled hardware software integration, resulting in best in class performance.
: Using or distributing these lists is a violation of privacy and, in many jurisdictions, illegal.
: Files shared with these naming conventions on public forums often contain "stealer logs" or are bundled with malware. If you attempt to download or open such files, you risk infecting your own system with trojans or ransomware.
: Turn on Multi-Factor Authentication (MFA) on all sensitive accounts to provide a layer of security that a simple password list cannot bypass. AI responses may include mistakes. Learn more
: Generate unique, complex passwords for every site to ensure that a leak on one platform doesn't compromise your entire digital identity.
: A "combo list" is a text file containing hundreds of thousands of username/email and password combinations. These are typically harvested from previous data breaches and are used by cybercriminals for "credential stuffing" attacks—automated attempts to log into various websites using the same credentials.
: Use Have I Been Pwned? to see if your email address has appeared in any known data leaks.
"Ready to improve your indoor air quality? Get in touch with us today to explore our certified IAQ solutions. Breathe easier, live healthier—contact us now!"
: Using or distributing these lists is a violation of privacy and, in many jurisdictions, illegal.
: Files shared with these naming conventions on public forums often contain "stealer logs" or are bundled with malware. If you attempt to download or open such files, you risk infecting your own system with trojans or ransomware.
: Turn on Multi-Factor Authentication (MFA) on all sensitive accounts to provide a layer of security that a simple password list cannot bypass. AI responses may include mistakes. Learn more
: Generate unique, complex passwords for every site to ensure that a leak on one platform doesn't compromise your entire digital identity.
: A "combo list" is a text file containing hundreds of thousands of username/email and password combinations. These are typically harvested from previous data breaches and are used by cybercriminals for "credential stuffing" attacks—automated attempts to log into various websites using the same credentials.
: Use Have I Been Pwned? to see if your email address has appeared in any known data leaks.