Tessa-model(2).rar 📥
Dr. Emma Taylor, a renowned data analyst, sat in front of her computer, staring at the screen with a mix of curiosity and concern. She had just received an anonymous email with a single attachment: "tessa-model(2).rar". The sender's email address was a jumbled mess of characters, offering no clues about who might have sent the file.
Emma's mind reeled with questions. What was the purpose of this AI? Who had created it, and why? And, most importantly, what had happened to Tessa all those years ago?
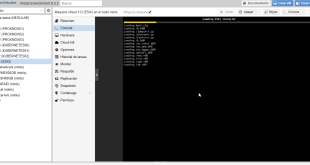
As Emma opened the archive, her computer beeped, warning her about potential risks. She hesitated for a moment before deciding to extract the contents. The archive contained a single file: "Tessa_Model_v2.exe". tessa-model(2).rar
The more Emma explored the model, the more she became convinced that this was no ordinary AI. The model's behavior and responses seemed to mirror Tessa's personality and wit, as if the AI had been trained on her friend's memories and experiences.
Emma's initial thought was that it could be a prank or a virus, but something about the filename caught her attention. "Tessa" was a name she hadn't heard in years – her old friend from college, Tessa, had been a brilliant mathematician who had worked on a top-secret project before mysteriously disappearing from the academic scene. The sender's email address was a jumbled mess
The story of "tessa-model(2).rar" had just begun, and Emma was determined to see it through to the end.
Emma realized that she had stumbled into something much bigger than herself. With the help of the Tessa model, she embarked on a perilous journey to uncover the truth, facing powerful forces that sought to keep the secrets buried. Who had created it, and why
As Emma delved deeper into the model, she began to unravel a complex web of secrets and conspiracies. She discovered that Tessa had been working on a revolutionary AI project, one that could change the course of human history. But the project's true intentions and the reasons behind Tessa's disappearance remained shrouded in mystery.

5 comentarios
Pingback: Laboratorio VMware Integrated Containers - VMware Blog
Pingback: Configuracion VMware Virtual Container Host - VMware Blog
Pingback: Crear docker en VMware - VMware Blog
Pingback: Migrar en VMware los VMkernel a switch distribuido - Blog VMware y Citrix
Pingback: Desinstalar plugin vSphere Integrated Containers - Blog VMware y Citrix